EHS Software.
Training.
Expertise.
Industry leading companies trust KPA software, training, and services for Environmental Health and Safety Compliance.
Top rated software in the industry

Deliver exceptional EHS
programs with less effort.
- Flexible EHS Software
Gain better visibility and efficiency through a comprehensive solution built by safety experts. - Online Training
Thousands of courses tailored to your industry and learning needs. - Consulting Services
Rely on 100+ credentialed EHS experts and 35+ years of experience and across our national network.
EHS Software
Your all in one solution for managing an effective EHS program.
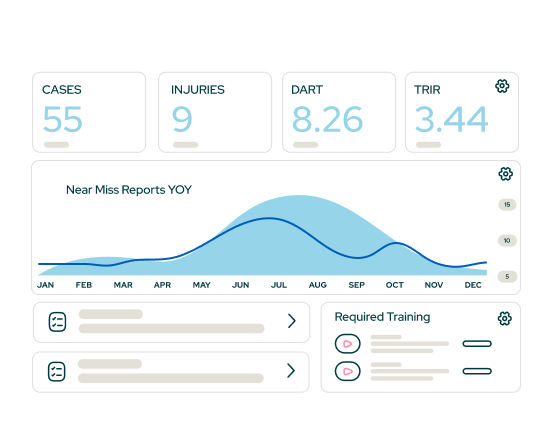
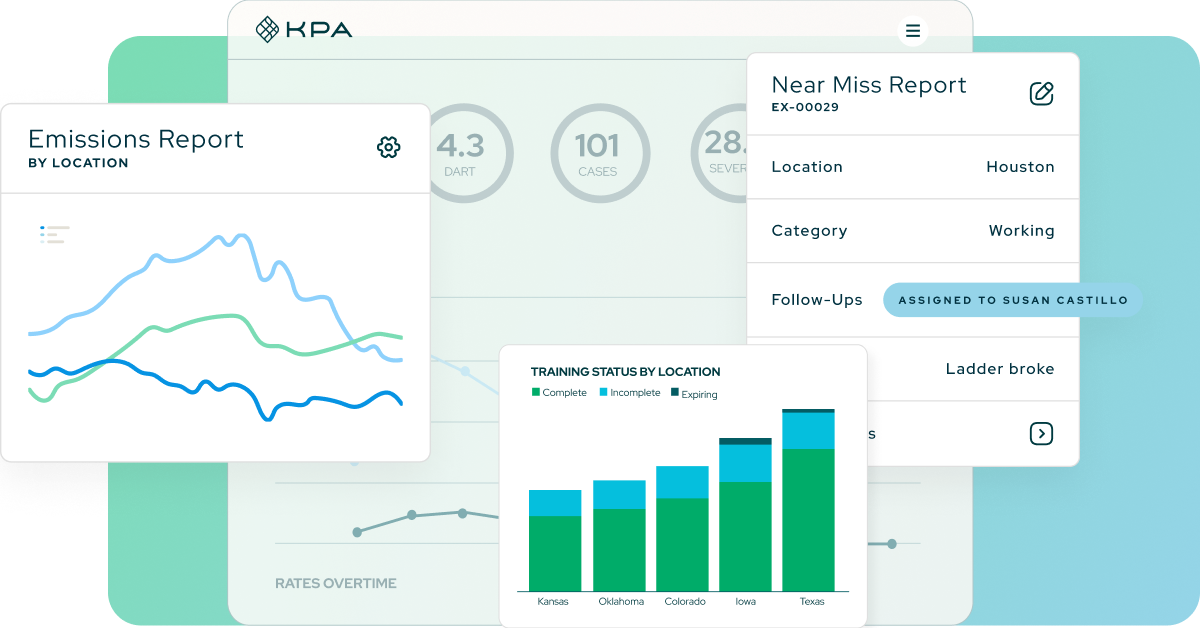
Designed for easy reporting & training in the field, providing real-time access to key components of your safety program.
Real-time incident management tools that give you the data you need to track incidents as they occur.
Comprehensive, award-winning library of over 1000 courses powered by an integrated Learning Management System.
Track and complete inspections for any type of asset. Make it easy with QR scanning technology.
ESG measurement, data management, and CO2 tracking to align with your sustainability initiatives.
Create measurable impact with KPA
Track results over time with configurable reports and dashboards.
70%
Decrease in Total Recordable Incident Rate (TRIR)
20%
Experience Modification Rating (eMOD) reduction
3x
Increase in productivity
90%
Reduction in paper and manual processes